Moving Beyond Technology

The Human Element – Introduction:
When it comes to cybersecurity, most people tend to think it’s all about technology. But guess what? It’s time to break that misconception. In today’s world, cyber threats the weakest link in the security chain is the human element.
You see, we may have fancy technologies, but there’s no magic bullet (despite what many vendors promise). No matter how much we invest in technology, we can still fall prey to cybercriminals who know just how to exploit our human nature.
The Conti ransomware gang hit the nail on the head last year when they said, “we also need to focus on the human part of our attacks. Our targets invest millions of dollars in security technologies, but they often overlook the human element. We will continue to exploit this weakness to our advantage.”” It’s a wake-up call to understand that in the traditional triad of People, Processes, and Technology, People are (and have been in probably the last 10 years) the center stage in cybersecurity.
So, buckle up and keep reading as we dive into the role of the human factor in cyber attacks.
The Exploitation of Human Vulnerabilities:
Cybercriminals are crafty. They know that humans are easier to manipulate than sophisticated security technologies. They also look for a ROI on their investments, so they will use whatever is the cheaper approach to reach their goal. So, they use psychological tricks like phishing and social engineering to exploit our weaknesses and gain unauthorized access to sensitive information. They send convincing email scams, impersonate trusted entities, and even dig up personal details from social media to trick us into revealing confidential data or compromising system security.
Still think that cybersecurity is all about fancy technology?
You took a look at the latest latest ENISA Threat Landscape. You saw that the top threats include ransomware and malware—definitely techie stuff. But guess who unwittingly lets those threats in? Yep, it’s people.
Now let me tell you, the Ponemon Institute’s Cost of Data Breach report is an eye-opener. In their “Initial attack vectors” section, they highlight the prevalence and cost of human-related attack vectors. Stolen or compromised credentials accounted for 19% of breaches, costing an average of $4.50 million. Phishing, at 16% of breaches, topped the list as the costliest initial attack vector, with an average cost of $4.91 million. Business email compromise was another initial vector among cyber attackers.
If you look closely, you’ll notice that every issue, even seemingly technical ones like “Vulnerability in third-party software,” ultimately comes down to human error. After all, who coded the software with the vulnerability or who didn’t define or apply a patching process? That’s right, a human.
Moving Towards a People-Centric Approach:
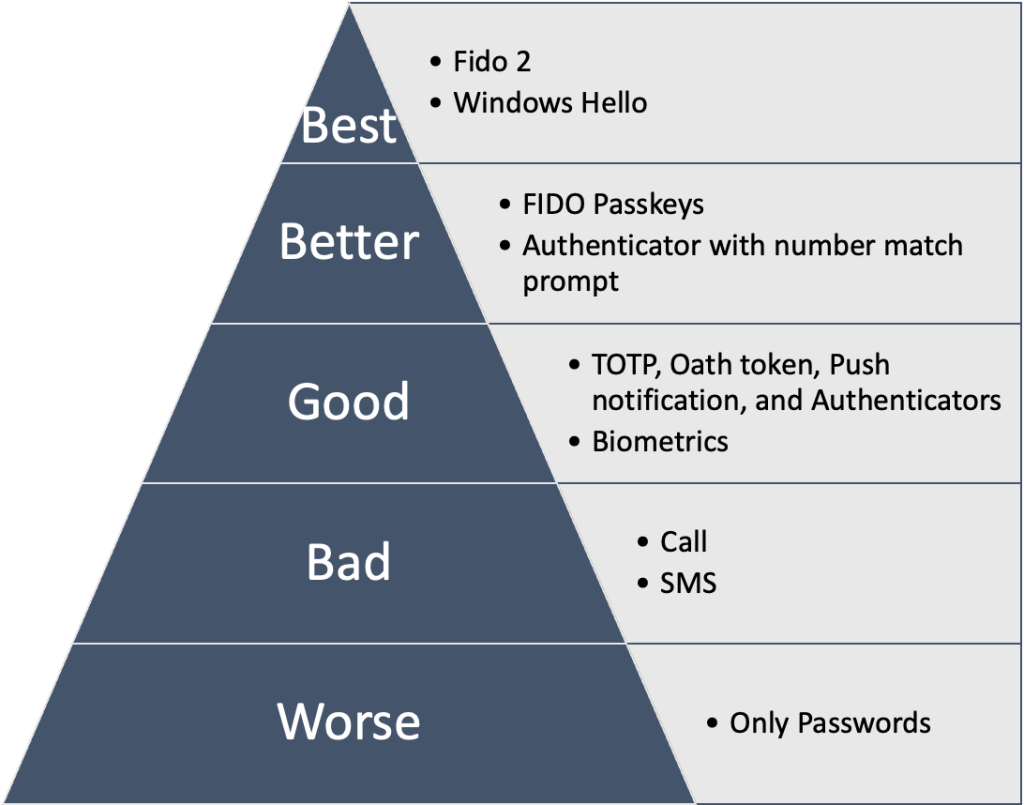
So, what can we do about it? Well, it’s time for organizations to start adopting a people-centric approach to cybersecurity. My recipe consist in building a “Cyber Culture”! This means understand what are the Cyber behaviors we want to influence, providing comprehensive training programs to raise cybersecurity awareness among employees and promoting a culture of vigilance and responsible behavior. We gotta teach everyday users about common cyber threats, show them how to spot suspicious activities, and encourage good practices like creating strong passwords and keeping software up to date.
But it’s not just about training. Organizations need to share real-world examples of cyber attacks, so people can see the real risks out there. By making everyone feel responsible for cybersecurity, we turn our workforce into a first line of defense against cyber threats.
And here’s a secret: investing in the human factor is not only cheaper, but it’s also way more effective than splurging on fancy technology. I mean, sure, we still need the right tools, but without a strong Cyber Culture, we’re like a castle with a moat but no guards. It just doesn’t work! I will write an article on this topic in the future.
So why isn’t a a People-Centric approach that widespread?
Many people still think that cybersecurity is all about technology. They believe it’s a technical issue that only (nerdy) IT folks (with glasses and a hoodie) can handle. The problem is that cybersecurity specialists often are really technical to start with so they neglect the crucial human elements.
And here’s another kicker: reporting lines within organizations often make things worse. Cybersecurity teams end up aligned with IT departments, who are mainly focused only on technical risks!
I know I’m digressing this is another topic: the need of having an effective, diverse and multidisciplinary Cyber team.
But the truth is, investing in Cyber Culture, in our people, is the key to success. It’s not only more cost-effective, but it’s also more impactful in preventing and mitigating cyber threats. So I think it’s time to break the cycle!
Conclusion:
it’s time we realized that cybersecurity is not just about technology. People play a crucial role, and cybercriminals know it. By adopting a people-centric approach, building a strong Cyber Culture, and empowering employees to be active defenders, organizations can level up their defense against cyber threats.
So, let’s remember that we’re not alone in this fight. It’s not just about fancy tech; it’s about us, the people. Together, we can create a safer digital world. Let’s do this!













Recent Comments