Safeguarding European Vulnerability Management
Following up on yesterday’s post, today we are publishing the full text of the open letter sent to ENISA and key European cybersecurity stakeholders.
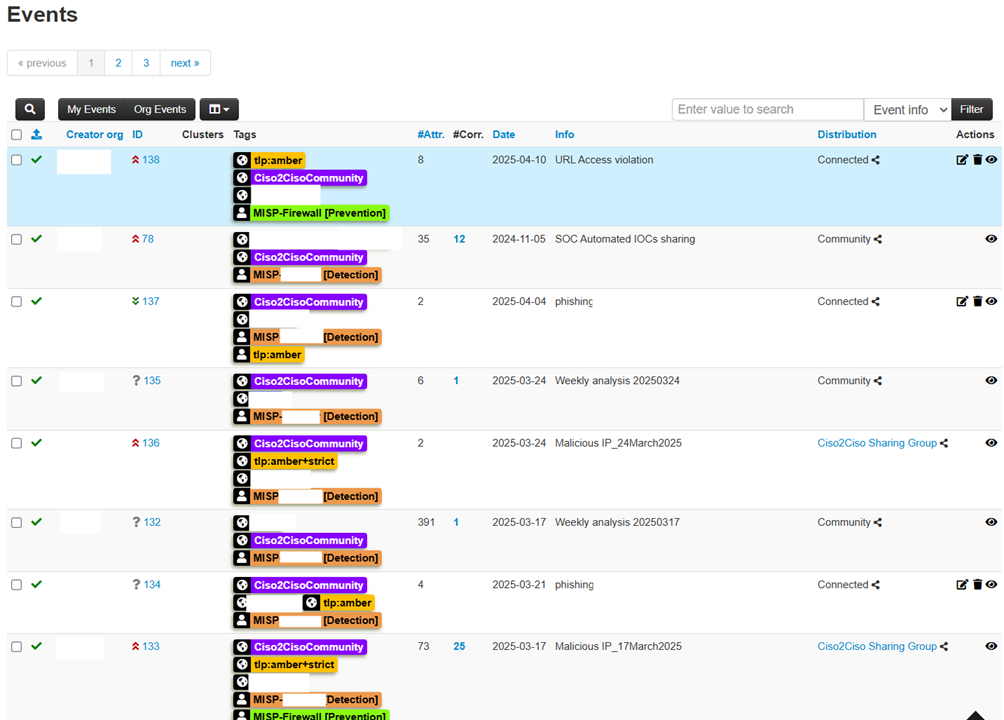
The letter addresses the urgent need for a reliable, independent European approach to vulnerability management in light of the recent MITRE announcement (see image below).
We invite the entire cybersecurity community to read, share, and support this initiative.
Open Letter Text
Subject: Open Letter to ENISA – Ensuring European Continuity and Governance for the CVE Program
To the attention of ENISA Management and to the EUVD team,
Dear ENISA Management and EUVD Team,
As representatives of various Italian CISO communities, we would like to express our sincere concern regarding the future of the CVE (Common Vulnerabilities and Exposures) program, as indicated in the recent communication from MITRE (source: https://bsky.app/profile/tib3rius.bsky.social/post/3lmulrbygoe2g).
The CVE program has long served as a cornerstone for global vulnerability identification, tracking, and coordinated response. Any disruption to this service would significantly impact European cybersecurity, affecting national vulnerability databases, tool vendors, incident response teams, and the protection of critical infrastructure, potentially reducing our collective capacity to respond effectively.
The recent announcement of the formation of the CVE Foundation (source: https://www.thecvefoundation.org/) — in response to the end of U.S. government sponsorship — represents an important moment for the global cybersecurity community. For 25 years, the CVE Program has been the pillar of vulnerability management, yet its future would benefit from broader international support.
We respectfully invite ENISA to consider assuming a European coordination role — at least temporarily — to develop a European alternative system that preserves existing CVE data while ensuring the continuity of these essential services —potentially through the integration and further development of the EUVD platform currently in beta phase. This would represent a reliable alternative, preventing future service interruptions and granting Europe independent governance over a capability of such critical importance.
We kindly ask ENISA to help safeguard the current CVE ecosystem and, drawing on the cross-disciplinary expertise of the undersigned associations, to explore possible improvements to the system for the benefit of the entire European community.
We would also recommend that ENISA establish direct contact with MITRE to explore avenues for collaboration and support, helping ensure that Europe remains an active and reliable partner in the global vulnerability management ecosystem.
As CISOs and as members of major Italian cybersecurity associations we declare our full availability to support ENISA and MITRE in any technical, operational, or advocacy capacity required.
We believe that Europe has an opportunity to take proactive steps to safeguard its digital resilience and avoid fragmentation. This aligns closely with the ongoing enhancements of cyber robustness and resilience promoted by multiple European directives and regulations.
We are ready to participate in any working groups, task forces, or initiatives that ENISA may wish to activate on this urgent matter.
This represents an important moment for European cybersecurity:
A coordinated response will strengthen our collective resilience and set a positive precedent for international cooperation.
We look forward to your response and remain at your disposal for further discussion.
Best regards,
Andrea Succi, creator of this initiative, on behalf of 45 Italian CISOs (or similar profiles) and of CISOs4AI https://cisos4ai.org/
Luca Moroni on behalf of CSA Cyber Security Angels https://cybersecurityangels.it/
Alessandro Oteri on behalf PensieroSicuro Network https://www.pensierosicuronetwork.it/
If you are interested in joining as a signatory or supporting this initiative, please let us know so we can include your name in future correspondence with ENISA.












Recent Comments